Hello,
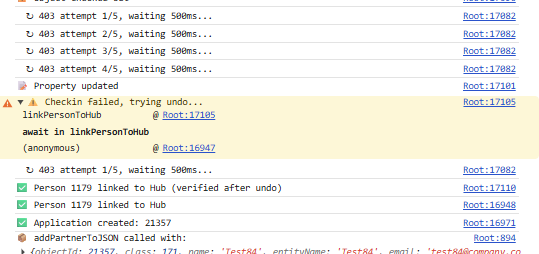
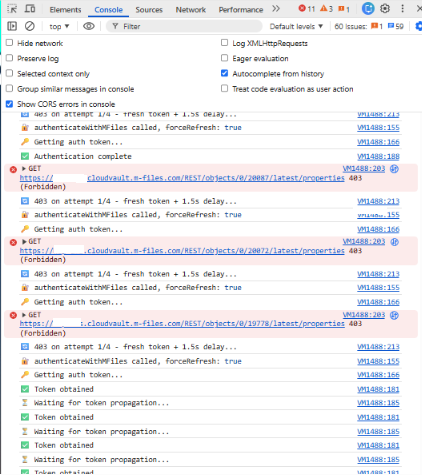
We have an api function in hubshare custom widget to link a person object to hub. It worked in POC (on-premise vault), but not in M-Files cloudvault (we have tried using retry to get through the 403 error on multi cloud server authentication problem.
We have tried sending cookies as per the article suggestion support.m-files.com/.../REST-API-and-Multi-Server-Mode-Session-management, but it's still not working (having a lot of 403s).
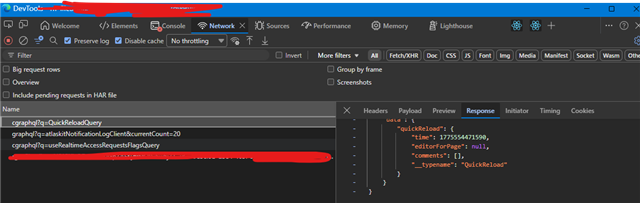
· Please see the attached screenshots:
Please suggest me any other solution for fix the 403 error's. Thanks!
Regards,
Senthil