Hi community and M-Files,
As we have multiple environments (dev, test, prod to name the standard ones), I am wondering about the best practice for moving/deploying configuration between those environments (especially NACLs). In our NACLs, we often have beside pseudo user security (metadata-driven security) also user groups (imported through AD). As we have different networks, those AD groups do have same names but obviously different domains. So for example on DEV, we have DEV\group1 and production we have PROD\group1.
We have currently developed everything on one network but now need to deploy it on other domains/networks. So my question or discussion point: what is the best practice to move vault configuration between different domains/networks, especially NACLs containing user groups, classes and views protected with user groups (different domains on different environments)?
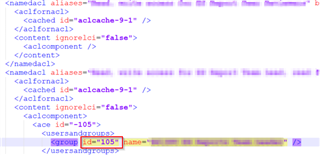
I have looked into exported values and could found how configuration of NACLs is built up (every NACL as unique identifier). One naïve approach would be to just replace domains with proper domains of deployment environment. On the other side, I see as well that it references user groups about unique ID that is probably generated when AD groups are first imported into M-Files. As we plan to import and sync AD groups manually on all environments and not move them through exporting function (those are different AD groups on different environments), they would get different unique IDs etc. So that would mean that I would need to update those unique references as well in exported config. This all seems very complicated and error prone.
Do you have an approach and experience with such a use case?
Thanks for great input.
Dejan